
95% of researchers rate our articles as excellent or good
Learn more about the work of our research integrity team to safeguard the quality of each article we publish.
Find out more
ORIGINAL RESEARCH article
Front. Phys. , 25 March 2025
Sec. Quantum Engineering and Technology
Volume 13 - 2025 | https://doi.org/10.3389/fphy.2025.1563674
This article is part of the Research Topic Advances in Quantum Technologies and Theoretical Progress in Quantum Information Processing Through Single-Photon Nonlinearity View all articles
In this paper, a mutual authentication quantum key agreement protocol with single-particle measurement is proposed. The participants can authenticate each other’s identity through their secret identity information and the entanglement property of Bell states. After the authentication phase, the participants can negotiate a private key with equal contribution. We prove that the proposed scheme is unconditional security. In comparison to the previous mutual authentication quantum key agreement protocols, the proposed method utilizes Bell states as the quantum resource states in both the identity authentication and key agreement stages. It requires single-particle measurement without the need for Bell measurements or the involvement of trusted or semi-trusted other participants. Additionally, our proposed scheme demonstrates significant advantages in terms of qubit efficiency.
As one of the important branches of cryptography, key agreement allows all the participants to contribute equally to generating a negotiated key, where any nontrivial subset cannot privately determine the negotiated key. Since the first key agreement protocol was proposed by Diffie and Hellman in 1976 [1], many key agreement protocols have been proposed [2–5]. However, with the rapid development of quantum computing and quantum computers, the classical cryptography schemes based on the complexity of mathematical algorithms will be seriously endangered. Different from classical cryptography, quantum cryptography is theoretically unconditionally secure. For this reason, quantum cryptography has garnered widespread attention from numerous cryptography researchers and has gradually evolved into a popular research direction in the field of cryptography.
Quantum cryptography encompasses various branches, such as quantum key distribution (QKD) [6–8], quantum key agreement (QKA) [9, 10], quantum secure direct communication (QSDC) [11–13], quantum secret sharing (QSS) [14, 15], quantum signature (QS) [16–18], quantum private query (QPQ) [19–21], quantum private comparison (QPC), [22–24]. Currently, quantum key agreement is a novel and highly significant research topic that has attracted considerable attention within the academic sphere.
In 2004, Zhou et al. [9], achieved the first QKA protocol by utilizing quantum teleportation, thereby pioneering the application of quantum technology in key negotiation. However, Tsai et al. [25] identified a critical flaw in Zhou et al.’s protocol, wherein a participant could unilaterally determine the shared key. Subsequently, in the same year, Hsueh et al. [26] proposed a QKA scheme using unitary operations and single photons. Nevertheless, Tsai et al. [27] pointed out that this scheme lacked sufficient security, as an attacker could acquire the shared key through controlled attacks without detection. In 2010, Chong et al. [10] successfully proposed an efficient two-party QKA protocol, building upon the foundation of the BB84 protocol. This QKA protocol primarily leverages unitary operations and delayed measurement techniques. Subsequently, numerous research efforts have been proposed to enhance the QKA protocol from various perspectives, such as multi-party QKA [28–32], improved communication efficiency [33–37], enhanced security [38, 39], and against noise environments [34, 40–44], semi-quantum capabilities [45–50].
However, the aforementioned QKA protocols lack the capability to authenticate the identities of the involved parties. In practical settings, attackers often attempt to impersonate participants to gain access to the shared key and carry out man-in-the-middle attacks on the QKA protocol. To counteract this attack, it is crucial to authenticate the identity of the key negotiators before the key establishment process, which holds significant importance for ensuring the security of the QKA protocol. In 2021, Zhu et al. [51] proposed a semi-honest three-party mutual authentication quantum key agreement (MAQKA) scheme based on three-particle entangled states, which requires a semi-honest third party to assist two key negotiators in achieving mutual authentication and key agreement. In the same year, Ma et al. [52] presented a MAQKA protocol based on five-particle entangled states, involving four participants and relying on two users to assist the other two users in achieving identity authentication and key agreement. However, this scheme exhibits relatively low qubit efficiency. In 2022, He et al. [53] presented a novel MAQKA protocol based on Bell states, which improves qubit efficiency and achieves the identity authentication and key agreement without relying on a trusted or semi-trusted third party.
In this paper, we propose a mutual authentication quantum key agreement protocol with single-particle measurement. The protocol utilizes Bell entangled states as the quantum source, enabling identity verification of participants before key agreement and against potential attacks. Compared to the previous MAQKA schemes, our proposed protocol has significant improvements in terms of quantum sources, auxiliary requirements from other participants, measurement bases, and qubit efficiency.
The rest of the paper is organized as follows. In Section 2, the proposed two-party mutual authentication quantum key agreement protocol is described in detail. In Section 3, we provide concrete examples. In Section 4, we analyze its security. In Section 5, we discuss the performance of our scheme and provide a conclusion.
Two participants Alice and Bob want to authenticate their identity and negotiate a key. We assume that Alice and Bob need a secret identity information
Step 1: Bell sates preparation and transmission. Alice prepares m + n Bell states all in
Step 2: Eavesdropping detection. After Bob received
Step 3: Mutual authentication. After the eavesdropping detection, the qubit sequence
Step 4: Key negotiation. After the mutual authentication phase, Alice and Bob negotiate a session key together. They calculate the value
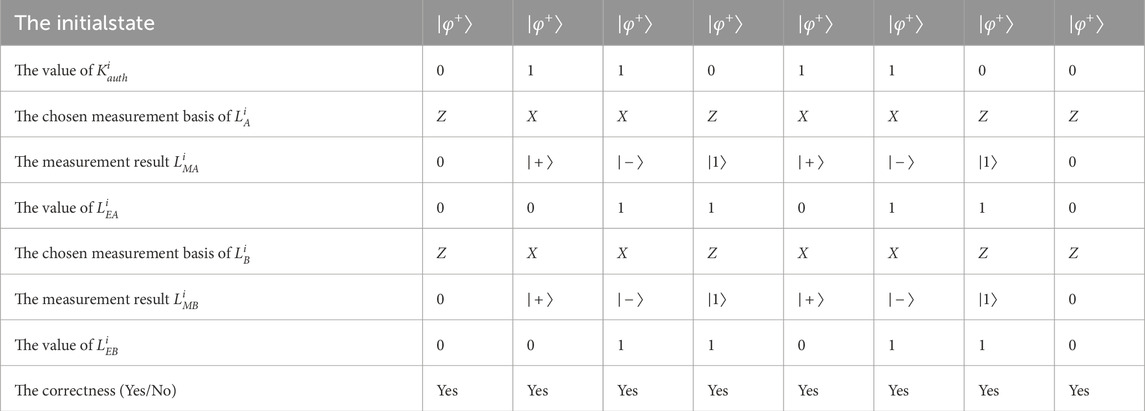
Table 1. The process of the mutual authentication phase when the identifies of Alice and Bob are legal.
As shown in Figure 1, the flowchart depicts the mechanism of the proposed protocol.
In this section, we provide concrete examples of our scheme to help readers better understand it. For simplicity, we have omitted the steps involved in eavesdropping detection.
Step 1: Bell states preparation and transmission. Alice prepares 16 Bell states all in
Step 2: Mutual authentication. For the qubit sequence
Step 3: Key negotiation. After the mutual authentication phase, Alice and Bob negotiate a session key together. They calculate the value
We analyze the security of mutual authentication phase from the following aspects.
Correctness: According to the process of the mutual authentication, Alice (Bob) can judge that the identity of Bob (Alice) is legal. If the identities of Alice and Bob are correct, they must have
Forgery attack: If charlie wants to disguise herself as Alice, she must get the correct value of
Unconditional security: In our scheme, the value of the hash function
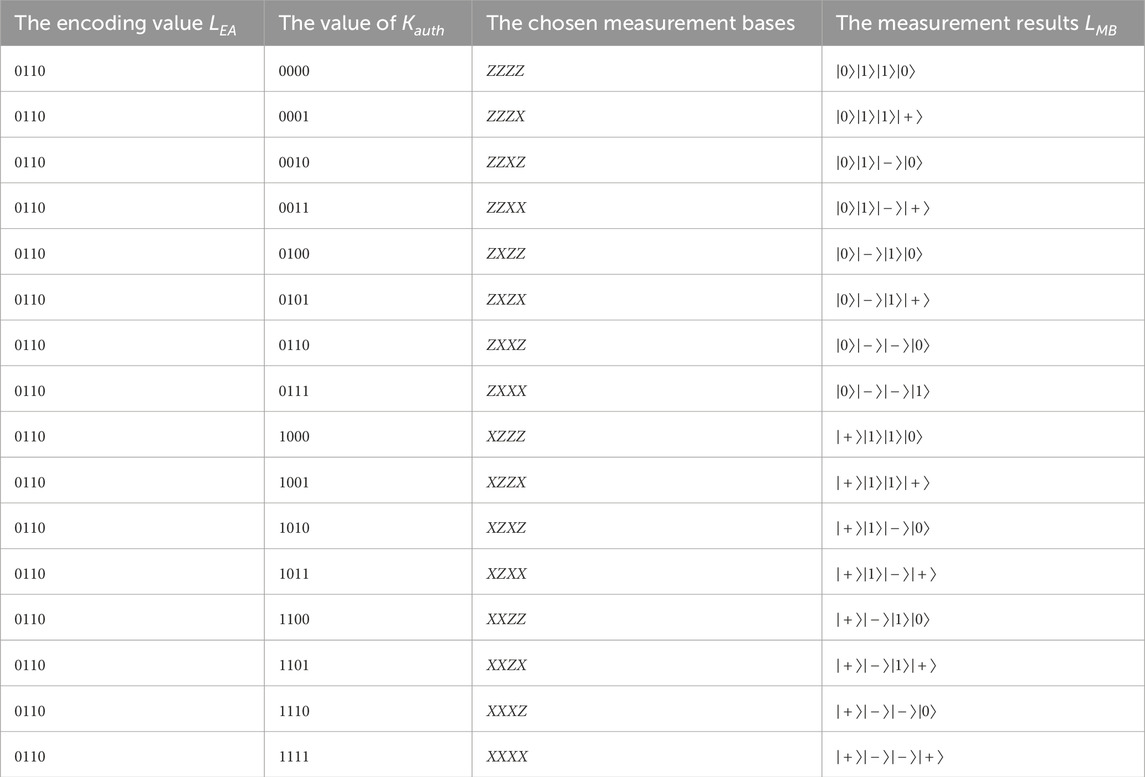
Table 3. The correlation among the encoding value
In this part, we analyze the participant attacks and the external attacks.
The participant attacks: The private key negotiation of our scheme is realized by the property of Bell states. The entanglement characteristic of Bell states ensures that the key negotiated by both parties is equal and random. Neither Alice nor Bob can change this randomness, so neither of them can independently control the private key. That is, they cannot successfully launch this attack.
The external attacks: Here, we consider four kinds of external attacks, including Trojan horse attacks, intercept-resend attack, measure-resend attack, and entangle-measure attack. As all the quantum states are transmitted only once, our scheme is naturally immune to the invisible photon eavesdropping Trojan horse attack [56] and the delay-photon Trojan horse attack [57]. Furthermore, in our scheme, we employ decoy states to detect the channel security, thereby ensuring the security of the transmitted qubit sequence
It should be noted that we use the information compression ability of the hash function
Thereby, the key negotiation of our scheme is unconditional security.
In this section, we discuss the performance of our scheme, and provide a conclusion.
As pointed in the reference [59], the qubit efficiency is defined as
In our protocol, from the perspective of the quantum source, our scheme utilizes Bell states, which are easier to implement with existing technology compared to three-particle entangled states [51] and five-particle entangled states [52]. Unlike scheme [52] that necessitates the involvement of a trusted or semi-trusted third party, and scheme [52] that relies on the assistance of two additional participants, our approach does not require auxiliary support from other participants. Furthermore, our scheme only requires single-particle measurement (
In this paper, we propose a mutual authentication quantum key agreement protocol with single-particle measurement. By utilizing the secret identity information and the entanglement property of Bell states, our protocol enables mutual identity authentication to be realized. After the authentication phase, the participants can negotiate a private key with equal contribution. We prove that our scheme is unconditionally secure and can resist potential attacks. In contrast to the previous MAQKA schemes, our proposed protocol has significant improvements in terms of quantum sources, assistance requirements from other participants, measurement bases, and qubit efficiency.
The original contributions presented in the study are included in the article/supplementary material, further inquiries can be directed to the corresponding author.
HY: Writing–original draft, Writing–review and editing. ZY: Writing–original draft, Writing–review and editing. SL: Writing–review and editing. MW: Writing–review and editing.
The author(s) declare financial support was received for the research, authorship, and/or publication of this article. This work is supported by the Major Research Plan of Hubei Province under Grant/Award NO. 2023BAA027; the Key Research & Development Plan of Hubei Province of China under Grant No. 2024BAB049 and the project of Science, Technology and Innovation Commission of Shenzhen Municipality of China under Grant No. GJHZ20240218114659027.
We are deeply grateful to all the authors for their steadfast guidance and support throughout the entire research process. Their valuable insights and encouragement are crucial in shaping the direction and quality of this research.
The authors declare that the research was conducted in the absence of any commercial or financial relationships that could be construed as a potential conflict of interest.
The author(s) declare that no Generative AI was used in the creation of this manuscript.
All claims expressed in this article are solely those of the authors and do not necessarily represent those of their affiliated organizations, or those of the publisher, the editors and the reviewers. Any product that may be evaluated in this article, or claim that may be made by its manufacturer, is not guaranteed or endorsed by the publisher.
1. Diffie W, Hellman M. New directions in cryptography. IEEE Trans Inf Theor (1976) 22:644–54. doi:10.1109/tit.1976.1055638
2. Steiner M, Tsudik G, Waidner M. CLIQUES: a new approach to group key agreement. In: Proceedings of the 18th international conference on distributed computing systems. Amsterdam, Netherlands (1998). p. 380–7. doi:10.1109/ICDCS.1998.679745
3. Steiner M, Tsudik G, Waidner M. Key agreement in dynamic peer groups. IEEE Trans Parallel Distrib Syst (2000) 11:769–80. doi:10.1109/71.877936
4. Pieprzyk J, Li CH. Multiparty key agreement protocols. IEEE Proc Comput Digital Tech (2000) 147:229–36. doi:10.1049/ip-cdt:20000531
5. Ateniese G, Steiner M, Tsudik G. New multiparty authentication services and key agreement protocols. IEEE J Sel Areas Commun (2000) 18(4):628–39. doi:10.1109/49.839937
6. Bennett CH, Brassard G. Quantum cryptography: public-key distribution and coin tossing. In: Proceedings of IEEE international conference on computers. Systems and signal processing. Bangalore, India (1984). p. 175–9.
7. Bennett CH. Quantum cryptography using any two nonorthogonal states. Phys Rev Lett (1992) 68:3121–4. doi:10.1103/physrevlett.68.3121
8. Boyer M, Kenigsberg D, Mor T. Quantum key distribution with classical Bob. Phys Rev Lett (2007) 99(14):140501. doi:10.1103/physrevlett.99.140501
9. Zhou N, Zeng G, Xiong J. Quantum key agreement protocol. Electron Lett (2004) 40(18):1149–50. doi:10.1049/el:20045183
10. Chong SK, Hwang T. Quantum key agreement protocol based on BB84. Opt Commun (2010) 283:1192–5. doi:10.1016/j.optcom.2009.11.007
11. Zhang W, Ding D-S, Sheng Y-B, Zhou L, Shi B-S, Guo G-C. Quantum secure direct communication with quantum memory. Phys Rev Lett (2017) 118(22):220501. doi:10.1103/physrevlett.118.220501
12. Panda SS, Yasir PA, Chandrashekar C. Quantum direct communication protocol using recurrence in k-cycle quantum walks. Phys Rev A (2023) 107(2):022611. doi:10.1103/physreva.107.022611
13. Hong YP, Zhou L, Zhong W, Sheng YB. Measurement-device-independent three-party quantum secure direct communication. Quant Inform Process (2023) 22:111. doi:10.1007/s11128-023-03853-1
14. Hillery M, Buek V, Berthiaume A. Quantum secret sharing. Phys Rev A (1999) 59:1829–34. doi:10.1103/physreva.59.1829
15. Senthoor K, Sarvepalli PK. Theory of communication efficient quantum secret sharing. IEEE Trans Inf Theor (2022) 68(5):3164–86. doi:10.1109/tit.2021.3139839
16. Gottesman D, Chuang I. Quantum digital signatures. arXiv:quant-ph/0105032 (2001). doi:10.48550/arXiv.quant-ph/0105032
17. Collins RJ, Donaldson RJ, Dunjko V, Wallden P, Clarke PJ, Andersson E, et al. Realization of quantum digital signatures without the requirement of quantum memory. Phys Rev Lett (2014) 113:040502. doi:10.1103/physrevlett.113.040502
18. Yin HL, Fu Y, Chen ZB. Practical quantum digital signature. Phys Rev A (2016) 93:032316. doi:10.1103/physreva.93.032316
19. Giovannetti V, Lloyd S, Maccone L. Quantum private queries. Phys Rev Lett (2008) 100(23):230502. doi:10.1103/physrevlett.100.230502
20. Gao F, Qin SJ, Huang W, Wen QY. Quantum private query: a new kind of practical quantum cryptographic protocol. Sci China Phys Mech Astron (2019) 62(7):70301. doi:10.1007/s11433-018-9324-6
21. Yang H, Xiao M. Multi-user quantum private query. Quan Inf. Process. (2020) 19:253. doi:10.1007/s11128-020-02732-3
22. Yang YG, Cao WF, Wen QY. Secure quantum private comparison. Phys Scr (2009) 80(6):065002. doi:10.1088/0031-8949/80/06/065002
23. Yang YG, Wen QY. An efficient two-party quantum private comparison protocol with decoy photons and two-photon entanglement. J Phys A: Math Theor (2009) 42(5):055305. doi:10.1088/1751-8113/42/5/055305
24. Geng MJ, Chen Y, Xu TJ, Ye TY. Single-state semiquantum private comparison based on bell states. EPJ Quan Technol. (2022) 9(36):36. doi:10.1140/epjqt/s40507-022-00156-9
25. Tsai C, Hwang T. On quantum key agreement protocol. Technical Report, C-S-I-E, NCKU, Taiwan ROC (2009)
26. Hsueh CC, Chen CY. Quantum key agreement protocol with maximally entangled states. In: Proceedings of the 14th information security conference (ISC 2004). Taipei, Taiwan: National Taiwan University of Science and Technology (2004). p. 236‖242.
27. Tsai CW, Chong SK, Hwang T. Comment on quantum key agreement protocol with maximally entangled states. In: Proceedings of the 20th cryptology and information security conference (CISC 2010). Hsinchu, Taiwan: National Chiao Tung University (2010). p. 210–3.
28. Shi RH, Zhong H. Multi-party quantum key agreement with bell states and bell measurements. Quan Inf Process (2013) 12:921–32. doi:10.1007/s11128-012-0443-2
29. Xu GB, Wen QY, Gao F, Qin SJ. Novel multiparty quantum key agreement protocol with GHZ states. Quan Inf Process (2014) 13:2587–94. doi:10.1007/s11128-014-0816-9
30. Yang H, Lu S, Zhu J, Wu J, Zhou Q, Li T. A tree-type multiparty quantum key agreement protocol against collusive attacks. Int J Theor Phys (2023) 62:7. doi:10.1007/s10773-022-05265-w
31. Liu B, Gao F, Huang W, Wen Q. Multiparty quantum key agreement with single particles. Quan Inf. Process. (2013) 12(4):1797–805. doi:10.1007/s11128-012-0492-6
32. Sun Z, Yu J, Wang P. Efficient multi-party quantum key agreement by cluster states. Quan Inf Process (2016) 15:373–84. doi:10.1007/s11128-015-1155-1
33. He YF, Ma WP. Quantum key agreement protocols with four-qubit cluster states. Quan Inf Process (2015) 14:3483–98. doi:10.1007/s11128-015-1060-7
34. Yang YG, Li BR, Li D, Zhou YH, Shi WM. New quantum key agreement protocols based on Bell states. Quan Inf Process (2019) 18:322. doi:10.1007/s11128-019-2434-z
35. Yang YG, Gao S, Li D, Zhou YH, Shi WM. Two-party quantum key agreement over a collective noisy channel. Quan Inf Process (2019) 18:74. doi:10.1007/s11128-019-2187-8
36. Huang X, Zhang SB, Chang Y, Qiu C, Liu DM, Hou M. Quantum key agreement protocol based on quantum search algorithm. Int J Theor Phys (2021) 60:838–47. doi:10.1007/s10773-020-04703-x
37. Zhao XQ, Wan H, Li LZ. High-efficient quantum key agreement protocol with entanglement measure. Int J Theor Phys (2022) 61:183. doi:10.1007/s10773-022-05166-y
38. Zhu ZC, Hu AQ, Fu AM. Improving the security of protocols of quantum key agreement solely using Bell states and Bell measurement. Quan Inf. Process. (2015) 14:4245–54. doi:10.1007/s11128-015-1110-1
39. Yang YG, Huang RC, Xu GB, Zhou YH, Shi WM, Li D. Measurement-device-independent quantum key agreement based on entanglement swapping. Quan Inf Process (2023) 22:438. doi:10.1007/s11128-023-04189-6
40. He YF, Ma WP. Two-party quantum key agreement against collective noise. Quan Inf Process (2016) 15:5023–35. doi:10.1007/s11128-016-1436-3
41. Gao H, Chen XG, Qian SR. Two-party quantum key agreement protocols under collective noise channel. Quan Inf Process (2018) 17:140. doi:10.1007/s11128-018-1910-1
42. Zhou YH, Wang MF, Shi WM, Yang YG, Zhang J. Two-party quantum key agreement against collective noisy channel. Quan Inf Process (2020) 19:100. doi:10.1007/s11128-020-2593-y
43. Li L, Zhou RG, Zhang XX. Three-party quantum key agreement protocol based on logical four-particle Cluster state to resist collective noise. Quan Inf Process (2023) 22:453. doi:10.1007/s11128-023-04206-8
44. Mu Q, Liu J, Wang Q, Li G, Sun W. Two-layer multiparty quantum key agreement protocol with collective detection. Int J Theor Phys (2024) 63:56. doi:10.1007/s10773-024-05564-4
45. Shukla C, Thapliyal K, Pathak A. Semi-quantum communication: protocols for key agreement, controlled secure direct communication and dialogue. Quan Inf. Process. (2017) 16:295. doi:10.1007/s11128-017-1736-2
46. Liu WJ, Chen ZY, Ji S, Wang HB, Zhang J. Multi-party semi-quantum key agreement with delegating quantum computation. Int J Theor Phys (2017) 56:3164–74. doi:10.1007/s10773-017-3484-6
47. Li HH, Gong LH, Zhou NR. New semi-quantum key agreement protocol based on high-dimensional single-particle states. Chin Phys B (2020) 29(11):110304. doi:10.1088/1674-1056/abaedd
48. Xu TJ, Gan ZG, Ye TY. Multiparty semiquantum key agreement with d-level single-particle states. Physica A: Stat Mech its Appl (2023) 625:128991. doi:10.1016/j.physa.2023.128991
49. Yi HM, Zhou RG, Xu RQ. Semi-quantum key agreement protocol using W states. Int J Theor Phys (2023) 62:212. doi:10.1007/s10773-023-05467-w
50. Hong WL, Bai CM, Zhang SJ, Liu L. Multiparty semi-quantum key agreement protocol based on multiparticle entangled states. Laser Phys Lett (2024) 21:125212. doi:10.1088/1612-202x/ad8cc5
51. Zhu H, Wang C, Li Z. Semi-honest three-party mutual authentication quantum key agreement protocol based on GHZ-like state. Int J Theor Phys (2021) 60:293–303. doi:10.1007/s10773-020-04692-x
52. Ma X, Hur J, Li Z, Zhu H. Quantum mutual authentication key agreement scheme using five-qubit entanglement towards different realm architecture. Int J Theor Phys (2021) 60:1933–48. doi:10.1007/s10773-021-04812-1
53. He YF, Pang Y, Di M. Mutual authentication quantum key agreement protocol based on Bell states. Quan Inf Process (2022) 21:290. doi:10.1007/s11128-022-03640-4
54. Zhang L, Han ZW, Ma QM, Li LL. Authenticated quantum key agreement based on cluster states against collective noise. Phys Scr (2024) 99:075104. doi:10.1088/1402-4896/ad514c
55. Zhang L, Han ZW, Li TH, Ma QY, Li LL. Authenticated multi-party quantum key agreement protocol based on cluster states. Laser Phys (2024) 34:095205. doi:10.1088/1555-6611/ad6d52
56. Cai QY. Eavesdropping on the two-way quantum communication protocols with invisible photons. Phys Lett A (2006) 351(12):23–5. doi:10.1016/j.physleta.2005.10.050
57. Li XH, Deng FG, Zhou HY. Improving the security of secure direct communication based on the secret transmitting order of particles. Phys Rev A (2006) 74:054302. doi:10.1103/physreva.74.054302
58. Gao F, Qin SJ, Wen QY, Zhu FC. Comment on: three-party quantum secure direct communication based on GHZ states. Phys Lett A (2008) 372:3333–6. doi:10.1016/j.physleta.2008.01.043
Keywords: quantum cryptography, quantum key agreement, mutual authentication, unconditional security, bell states, single particle measurement
Citation: Yang H, Yi Z, Lu S and Wang M (2025) Mutual authentication quantum key agreement protocol with single-particle measurement. Front. Phys. 13:1563674. doi: 10.3389/fphy.2025.1563674
Received: 20 January 2025; Accepted: 03 March 2025;
Published: 25 March 2025.
Edited by:
Ming Yang, Anhui University, ChinaReviewed by:
Tianyu Ye, Zhejiang Gongshang University, ChinaCopyright © 2025 Yang, Yi, Lu and Wang. This is an open-access article distributed under the terms of the Creative Commons Attribution License (CC BY). The use, distribution or reproduction in other forums is permitted, provided the original author(s) and the copyright owner(s) are credited and that the original publication in this journal is cited, in accordance with accepted academic practice. No use, distribution or reproduction is permitted which does not comply with these terms.
*Correspondence: Songfeng Lu, bHVzb25nZmVuZ0BodXN0LmVkdS5jbg==
†These authors have contributed equally to this work.
Disclaimer: All claims expressed in this article are solely those of the authors and do not necessarily represent those of their affiliated organizations, or those of the publisher, the editors and the reviewers. Any product that may be evaluated in this article or claim that may be made by its manufacturer is not guaranteed or endorsed by the publisher.
Research integrity at Frontiers

Learn more about the work of our research integrity team to safeguard the quality of each article we publish.